In today’s connected world, your Google Account is often the digital hub for your emails, photos, files, and browsing activity. With so much personal information flowing through it, keeping your account private and secure isn’t just an option—it’s essential. Fortunately, Google provides powerful built-in tools to help you safeguard your information, and one of the most effective is the Google Privacy Checkup.
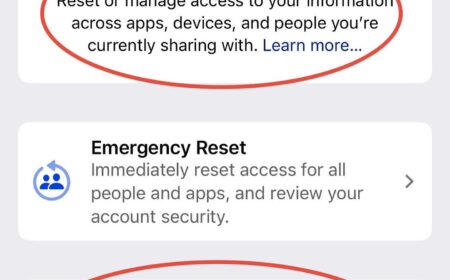
iPhone Privacy Tip: Run a Safety Check
Your iPhone has built-in privacy and security tools that let you see who and what has access to your data, location, and accounts. A quick Safety Check can give you peace of mind and control over your digital footprint.
Android Privacy: A Step-by-Step Setup
Want tighter privacy on Android without ditching Google entirely? Below is a practical walkthrough—based on the exact screens you shared—to reduce data collection, ad targeting, and accidental exposure while keeping core services usable.
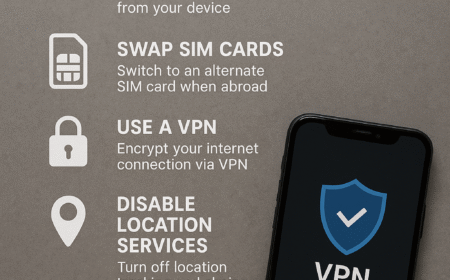
Mobile Device Privacy and Discretion for Travelers
Traveling with smartphones comes with hidden risks. Whether at home or abroad, your phone constantly emits signals, stores personal data, and may leave a digital trail that compromises your privacy. This guide highlights simple but effective steps to keep your device secure and your movements discreet.
Cyber Security 101 – Securing Your Home Wi-Fi
With more and more people conducting business at home, employees working remotely and even CEOs running companies from their residences, it is no surprise the FBI has reported a more than 300% increase in cyber crimes since COVID began. This article is intended to discuss the very basics of cyber security that we can apply to our homes to make us more secure.
Mobile Device Security and Privacy: Best Practices for Minimizing Exposures
The majority of attacks on mobile devices focused on human exploitation, as found in the Proofpoint Human Factor Report. Basically, various messages, mainly emails, were sent with malicious attachments or links that relied on human actions or responses to initiate the breach, rather than technically infiltrating a system directly. This being the case, increasing your knowledge and awareness is going to be the best preventative action you can take to safeguarding your information.