The majority of attacks on mobile devices focused on human exploitation, as found in the Proofpoint Human Factor Report. Basically, various messages, mainly emails, were sent with malicious attachments or links that relied on human actions or responses to initiate the breach, rather than technically infiltrating a system directly. This being the case, increasing your knowledge and awareness is going to be the best preventative action you can take to safeguarding your information.
Mobile device attacks are an increasing problem as hackers begin to target mobile devices over desktop computers. For most working people, your entire life is on your phone. Not only limited to financial data, but your professional information and your day to day life events. Because of this, attackers choose to attack mobile devices more than any other. “We see all major mobile OSs being impacted, from Android, Apple iOS, Windows phone via BlackBerry to Symbian, with the ultimate aim being persistent remote control of the end user’s device.” – Simon Mullis, global technical lead at FireEye
Below are some of the best practices for ensuring the security of your data on your mobile device.
–
C3P2R
Firstly, let’s keep it simple, but very effective – remember C3P2R (C three P two R). Here’s what it stands for:
- Control:
- Keep your device in your possession to avoid tampering.
- Charging:
- Use known charging cables and sources; avoid public USB ports, etc.
- Connections:
- Connect only to trusted networks; avoid unprotected or public Wi-Fi, Bluetooth, etc.
- Passwords:
- Use strong, unique passwords, change them yearly, and enable multi-factor authentication for sensitive logins.
- Permissions:
- Regularly review app permissions to minimize unnecessary access to sensitive data, location, microphone, etc.
- Resets:
- Perform regular device factory resets annually.
–
Physical Security & User Authentication
The first line of defense of a technical device is the physical security of the hardware. Device loss and theft constitutes most common “breach” of mobile devices. For example, a trusted employee leaving a phone exposed on a bus and it gets grabbed in an instant. User authentication protocols and password protection help limit the risks and dangers of a lost device. Enabling data wiping for repeated false attempts to access and even a remote wiping capability is recommended, and naturally so is regular backing up of your data to reduce loss. In short, don’t get lazy or complacent; ensure you use strong passwords and other user authentications to protect your device from simple intrusion.
–
Cyber Security 101: Securing Your Home
–
Do not Jailbreak/Root Your Device
While jailbreaking your device can enable you to use almost anything you want, including unverified apps, many of said apps have security vulnerabilities. In fact, the number one indicator of your phone being compromised is the status of the OS and if it has been jailbroken. Additionally, the overwhelming majority of technical attacks on Apple’s iOS only affect jailbroken devices. In other words, avoid the urge to customize your device beyond what the designers intended; don’t overwind your toys.
–
Consider using a secure messaging app
There are many options out there for 3rd party messaging apps, however very few can compete with Signal or Threema for overall security. They are designed to generate as little data on servers as possible, offer best-in-class encryption and Threema even offers anonymity through a random Threema ID – no phone number or email address is required in order to use it and is a 100% independent and self-financed company in the heart of Switzerland with its own servers and in-house software development.
–
Update Your OS Regularly to Get the Latest Security Patches
Although it may get tedious, update your OS and Apps whenever available to ensure any gaps in security are plugged by the newest updates. Along with software updates and added features, security updates are a primary reason for such updates, take advantage of these to resolve emerging threats and limit exposures.
INFOGRAPHIC: Surprising stats exposing mobile data dangers
–
Avoid Unknown Networks and Reduce Connectivity
A very effective and simple way to minimize potential access by hackers is by limiting the amount of time you have with open connectivity, such as what is offered when you have your Wi-Fi or Bluetooth enabled. While this is a very technical and difficult approach, the ease in reducing this risk is worth it.
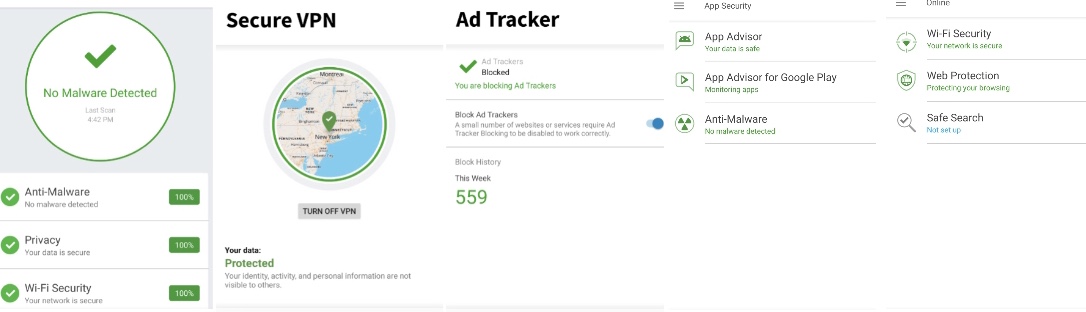
The other danger is rogue Wi-Fi networks which may be hackers intending to lure people in by logging on at public locations. The SSID (the name of the network) is easily cloned to read “Airport WiFi” or something else seemingly harmless, but don’t be fooled and only connect to known networks. Also, consider using encryption if any sensitive data is stored on the phone as well as for data in transit with more secure technologies, such as a Virtual Private Network (VPN). (Setting up a VPN for iPhone – Setting up a VPN for Android) An excellent VPN option for IOS/Android/PC/Mac/tablets is Norton VPN and there mobile security products are also highly recommended, and now couple with LifeLock – read more here.
–
–
Be Careful Not to Fall for Phishing Schemes
Avoid potential phishing scams, virus schemes and malware threats by not clicking on unknown or unrequested links. Do not open e-mail attachments from ANY source that you have not identified or asked for attachments from. Additionally, verify the source of the attachment and do not trust the name as masquerading as an associate or legitimate company is easy and common.
–
Carefully Select Which Apps you Download
Mobile device users willingly downloaded over 2 billion mobile apps in 2015 that stole their personal information and corrupted their device. Malicious apps can be disguised as social media apps or mobile entertainment apps to trick users into choosing this version and infecting their own systems willfully. Ensure the app you choose to download is the legitimate version, from a legitimate provider.
In a recent study by NowSecure, 24.7 percent of mobile apps include at least one high-risk security flaw, the average device connects to 160 unique IP addresses every day, 35 percent of communications sent by mobile devices are unencrypted, business apps are three times more likely to leak login credentials than the average app, and games are one-and-a-half times more likely to include a high risk vulnerability than the average app.
–
Consider Using a Secure WiFi Service
Especially when traveling, using hotel or airport WiFi can be the most at-risk times for your data. Using your own WiFi service is a great way to secure your data and privacy, such as the SkyRoam Solis.
–
Use Strong Passwords and use a Password Protector
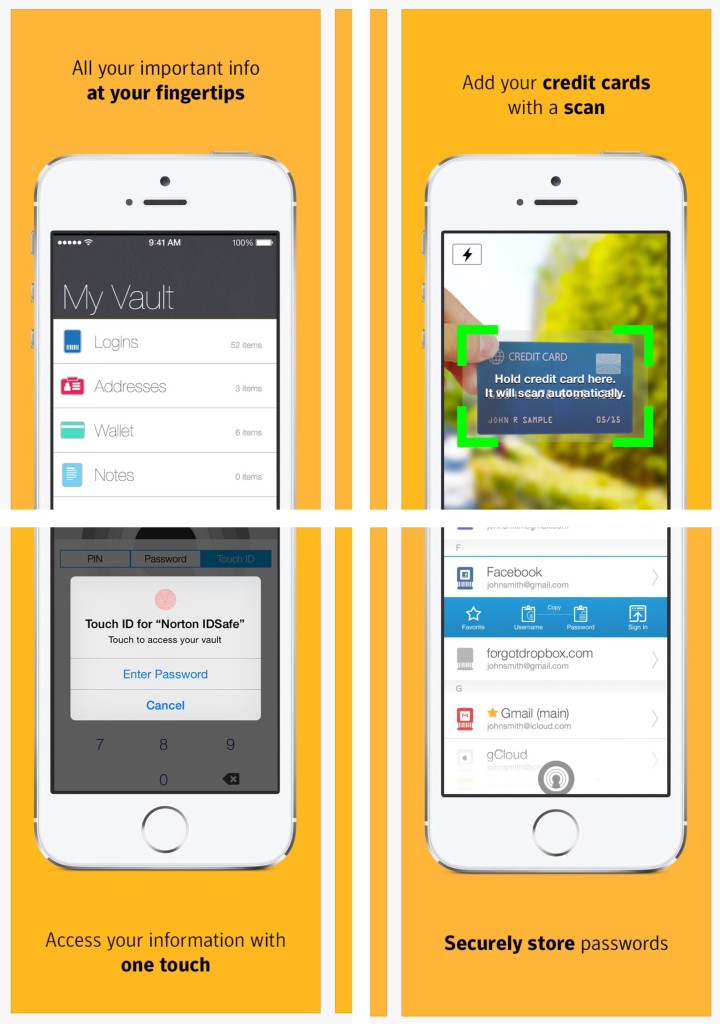
Passwords and pin codes are not the best way to secure data by any means, but that is no reason to make it easy for attackers by using pin codes like ‘1234’ or passwords like ‘password.’ Simple things you can do go a long way, like using a password creator and storage stool. Passwords should also be changed regularly. A very simple password technique for both creating a strong password and ensuring this change is this: identify a date 30-90 days in advance, creating a password from the dates combination, such as March15@)!* (the month of May with a capital letter, the day in numbers and the year in special characters) with this method, you have a strong password that encourages you to update it when that date comes around, and alternate how you order and type in the month, day and year.
–

–
Use Data Blocking Tools
Simple tools, such as a webcam cover, a microphone blocker and a USB data blocker can be extremely useful if your devices are compromised or if you are connecting to a unknown charger, etc. (absent a better choice.)
–
Digital Trails: Why Bodyguards Must Manage Their Own Devices
–
Mobile Device Privacy Settings Guide
iPhone Privacy Tools & Settings (iOS 15+)
- App Privacy Report
- What it does: Logs which apps access your mic, camera, location, contacts, etc.
- Where: Settings → Privacy & Security → App Privacy Report
- Mail Privacy Protection
- What it does: Hides your IP and prevents email senders from knowing when you open messages.
- Where: Settings → Mail → Privacy Protection
- Hide My Email
- What it does: Creates random email aliases to forward to your inbox.
- Where: Settings → Apple ID → iCloud → Hide My Email
- Private Relay (iCloud+)
- What it does: Hides your IP address and encrypts Safari traffic.
- Where: Settings → Apple ID → iCloud → Private Relay
- App Tracking Transparency (ATT)
- What it does: Requires apps to ask permission before tracking you.
- Where: Settings → Privacy & Security → Tracking
- Location Services Controls
- What it does: Limits app access to location (always/while using/never) + approximate vs. precise.
- Where: Settings → Privacy & Security → Location Services
- Microphone/Camera Access Indicators
- What it does: Shows a green or orange dot when either is in use.
- Where: Enabled by default in Control Center.
- Safari Privacy Features
- Features:
- Intelligent Tracking Prevention
- Prevent cross-site tracking
- Privacy Report (shows blocked trackers)
- Where: Settings → Safari
- Features:
- Password Monitoring
- What it does: Alerts you if saved passwords are compromised.
- Where: Settings → Passwords → Detect Compromised Passwords
–
Android Privacy Tools & Settings (Android 12+)
- Privacy Dashboard
- What it does: Shows a timeline of app access to location, camera, mic, etc.
- Where: Settings → Privacy → Privacy Dashboard
- Microphone & Camera Toggles
- What it does: Global switch to turn off mic and/or camera access.
- Where: Quick Settings or Settings → Privacy
- Approximate Location
- What it does: Lets apps see your general location only.
- Where: App Permissions → Location → Change to “approximate”
- Permission Manager
- What it does: View and control which apps have access to various sensors/data.
- Where: Settings → Privacy → Permission Manager
- One-Time Permissions
- What it does: Lets you grant temporary access to location, mic, or camera.
- Where: Appears during permission prompt.
- Auto-Reset Permissions
- What it does: Automatically removes app permissions after inactivity.
- Where: Settings → Apps → App Info → Permissions
- Google Account Privacy Settings
- Features:
- Ad personalization controls
- Web & app activity history
- Location history
- YouTube history
- Where: Settings → Google → Manage your Google Account → Data & Privacy
- Features:
- Android Private Compute Core
- What it does: Keeps AI-powered features (like Smart Reply) private on device.
- Where: Background service (available on Pixel and Android 12+)
- Guest Mode / Multiple Users
- What it does: Lets you share your phone without giving access to your data.
- Where: Settings → System → Multiple users
- Secure Folder (Samsung) / App Lock (OEM-dependent)
- What it does: Isolates sensitive files, apps, and data with biometric lock.
- Where: Samsung: Settings → Biometrics & Security → Secure Folder
–
———————————————————————
Joseph M. LaSorsa, CPP® is currently employed as a senior partner managing and conducting: Protective Operations Training Courses, Executive Protection & Bodyguard Services, Risk Management Consultations & Seminars, Workplace Violence Prevention Seminars & Intervention Services, Security Consultations & Seminars, Private Investigations and Technical Surveillance Counter-Measures with LaSorsa & Associates – an International Protection, Investigations & Consulting Firm.